In Part 1, we covered how the WeilChain Audit SDK adds cryptographic identity and verifiable logging to backend LLM agent frameworks. Part 2 extended the same primitive to CLI and IDE-based systems like Claude Code. In Part 3, we show how using the WAuth Wallet browser extension, every interaction can produce a verifiable on-chain receipt for browser-based LLMs — including ChatGPT and Claude.
This document focuses on architecture and execution flow.
1. Problem: Browser AI Has No Verifiable Trace
When using browser-hosted AI, prompts are sent via HTTPS, responses are rendered in the DOM, no user-controlled identity is attached, and no immutable audit trail exists.
Even if providers log internally, the user cannot independently verify, cannot cryptographically prove, and cannot export tamper-proof history.
We solve this by inserting a user-controlled identity layer in the browser.
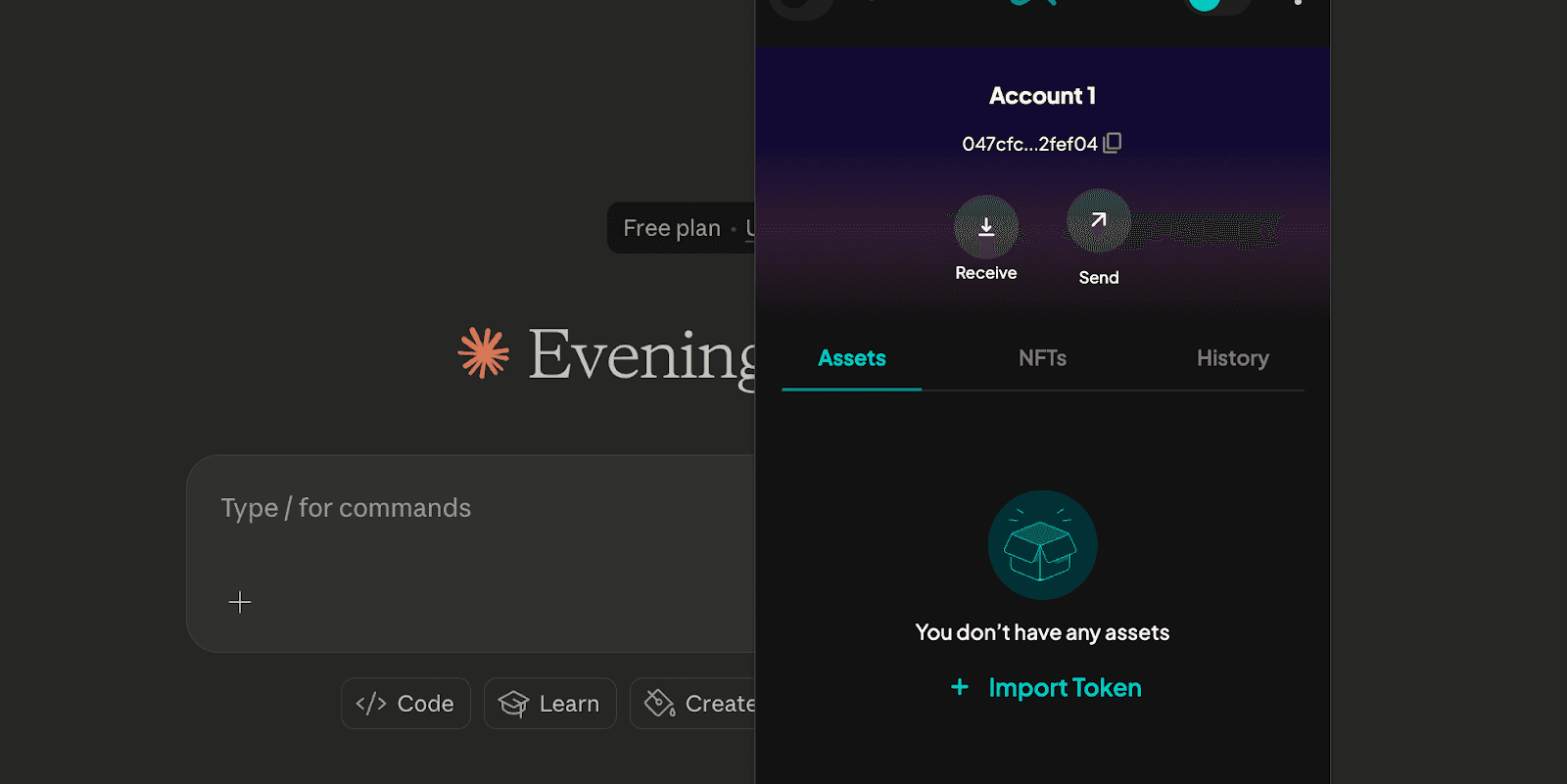
2. WAuth Wallet: Browser-Based Identity
WAuth is a browser extension that stores a WeilChain private key, exposes signing capability to the web context (with permission), and anchors signed audit entries on WeilChain.
The wallet provides persistent identity per user, address-bound audit trail, and non-repudiation of interactions.
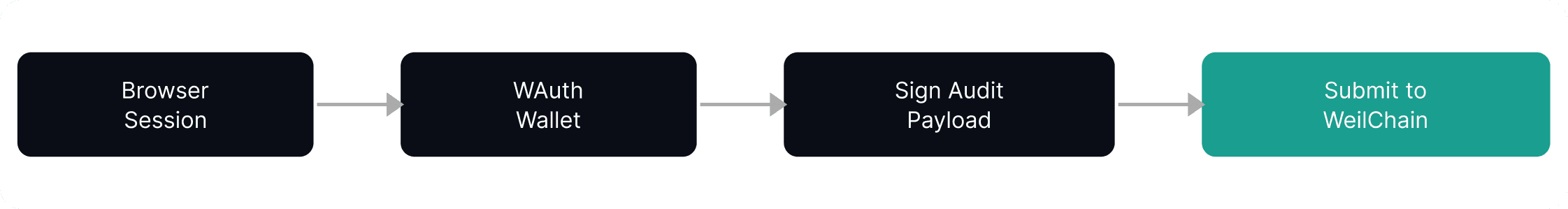
3. System Architecture
This uses the same audit mechanism described in Part 1: serialize, hash, sign, broadcast, and store an immutable record. No changes required from OpenAI or Anthropic.
4. What Gets Audited?
Every interaction captures three things:
Prompt Submission
{
"event": "user_prompt",
"provider": "chatgpt",
"model": "gpt-4o-mini",
"prompt_hash": "0xabc..."
}
Model Response
{
"event": "model_response",
"response_hash": "0xdef..."
}
Metadata including timestamp, page URL, conversation ID (if accessible), and user wallet address.
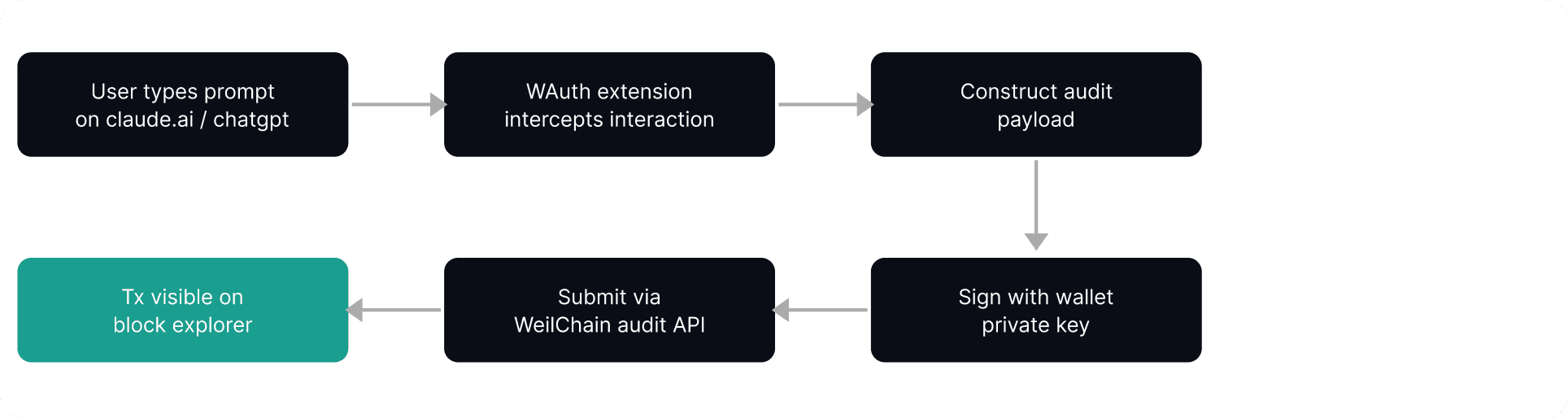
5. How the Extension Works Technically
Step 1 — Permission Model
The extension requires access to claude.ai and chatgpt.com, permission to inject content scripts, and permission to access the WAuth signing API. No cross-site tracking — only AI interaction domains are monitored.
Step 2 — DOM / Network Observation
The extension detects prompt input submission, network requests to the provider API, and streaming response completion. It constructs a canonical audit object:
Step 3 — Signing
WAuth serializes the payload, signs it with the private key, and returns a signature and address.
Step 4 — Broadcast
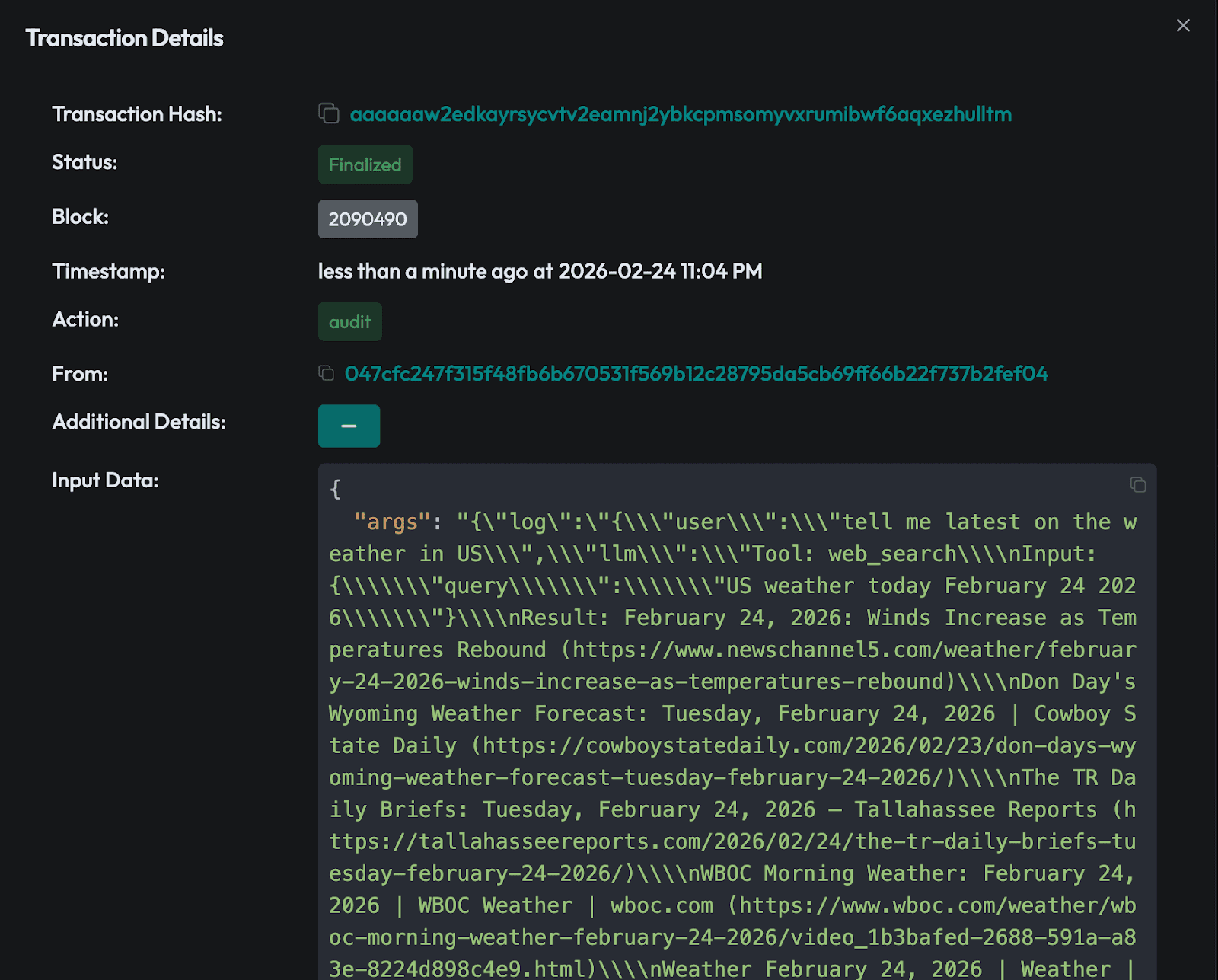
The extension calls the audit transaction with the payload hash, signature, and wallet address. WeilChain records the agent/user address, hash, signature, timestamp, and transaction ID.
6. Identity Model in Browser Context
Unlike backend agents, here the human user is the identity — the wallet lives in the browser and all interactions are attributed to that address. This enables portable AI interaction history, proof of authorship of prompts, proof of AI-generated content origin, and an on-chain audit trail for regulated use cases.
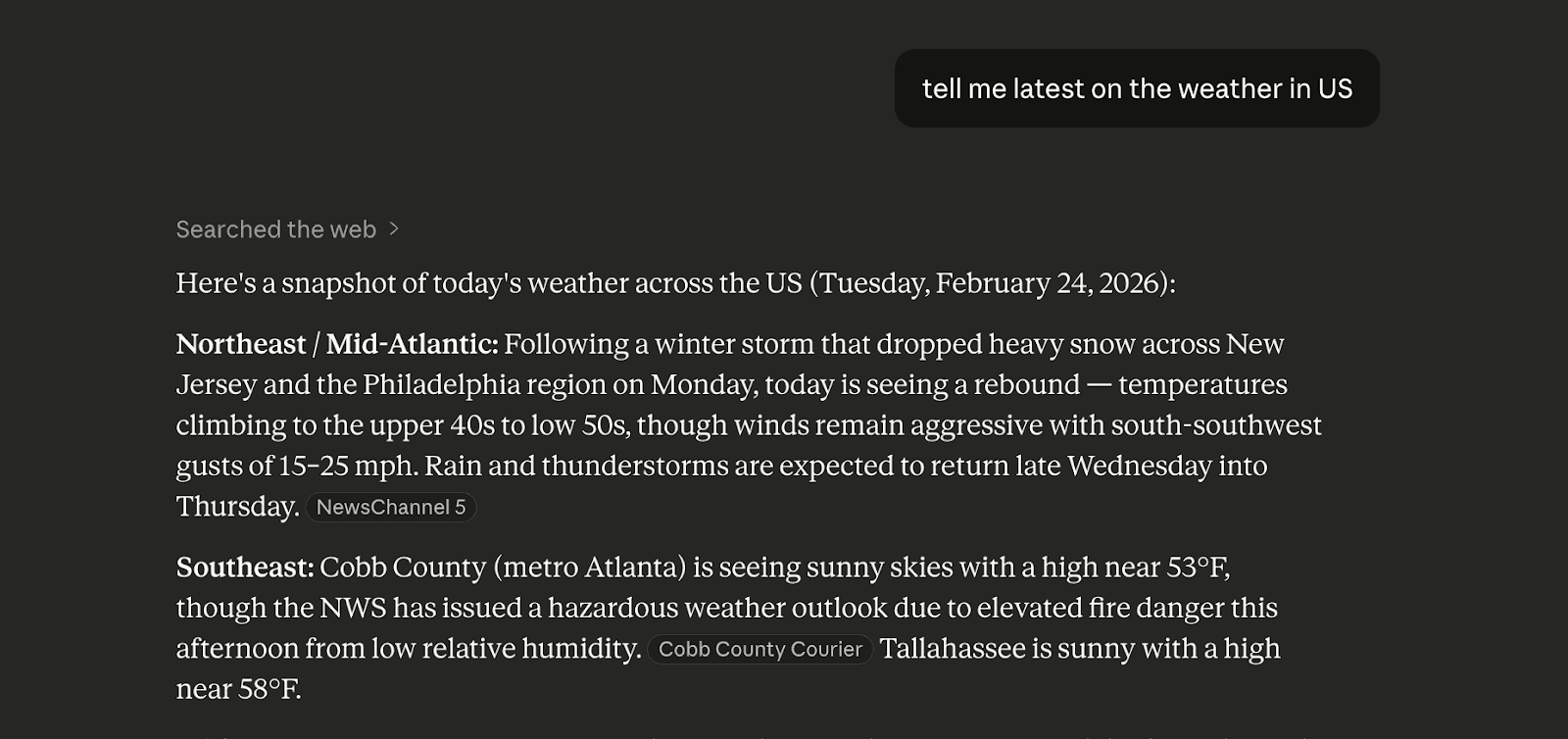
7. Viewing Receipts
Every audit call results in a transaction. Users can open the WeilChain block explorer at marauder.weilliptic.ai, search by wallet address, and view chronological interaction logs. This provides public verifiability, an immutable timeline, and third-party auditability.
8. Enterprise Use Cases
Receipts unlocks verifiable AI interactions for financial advisory workflows, legal AI drafting systems, AI-assisted contract negotiation, compliance-heavy industries, and AI-driven trading or research systems. Each interaction becomes provable.
Summary
To enable Receipts for Claude or ChatGPT: install the WAuth browser extension, grant domain permission, use AI normally, and the extension auto-audits interactions. View transactions on the WeilChain explorer.
Same audit mechanism. Same signature model. Same blockchain anchoring. No provider integration required.
With WAuth, AI interaction gains identity, identity gains cryptographic signature, and signature gains blockchain anchoring. Browser-based AI becomes auditable.
Not logs. Receipts.